· Security · 4 min read
Leveraging EPSS in Practice: A Strategic Framework for Vulnerability Prioritization
Strategic Data Driven Risk Reduction

Transform Your Security Posture with EPSS-Powered Vulnerability Prioritization
In today’s rapidly evolving threat landscape, vulnerability management has become increasingly complex. With hundreds of new CVEs published each month, security teams need effective methods to separate signal from noise. Exploit Prediction Scoring System (EPSS) provides a powerful, evidence-based approach to vulnerability prioritization—but how can we translate these probability scores into actionable security protocols? This article explores a practical implementation framework that turns EPSS insights into concrete operational guidance.
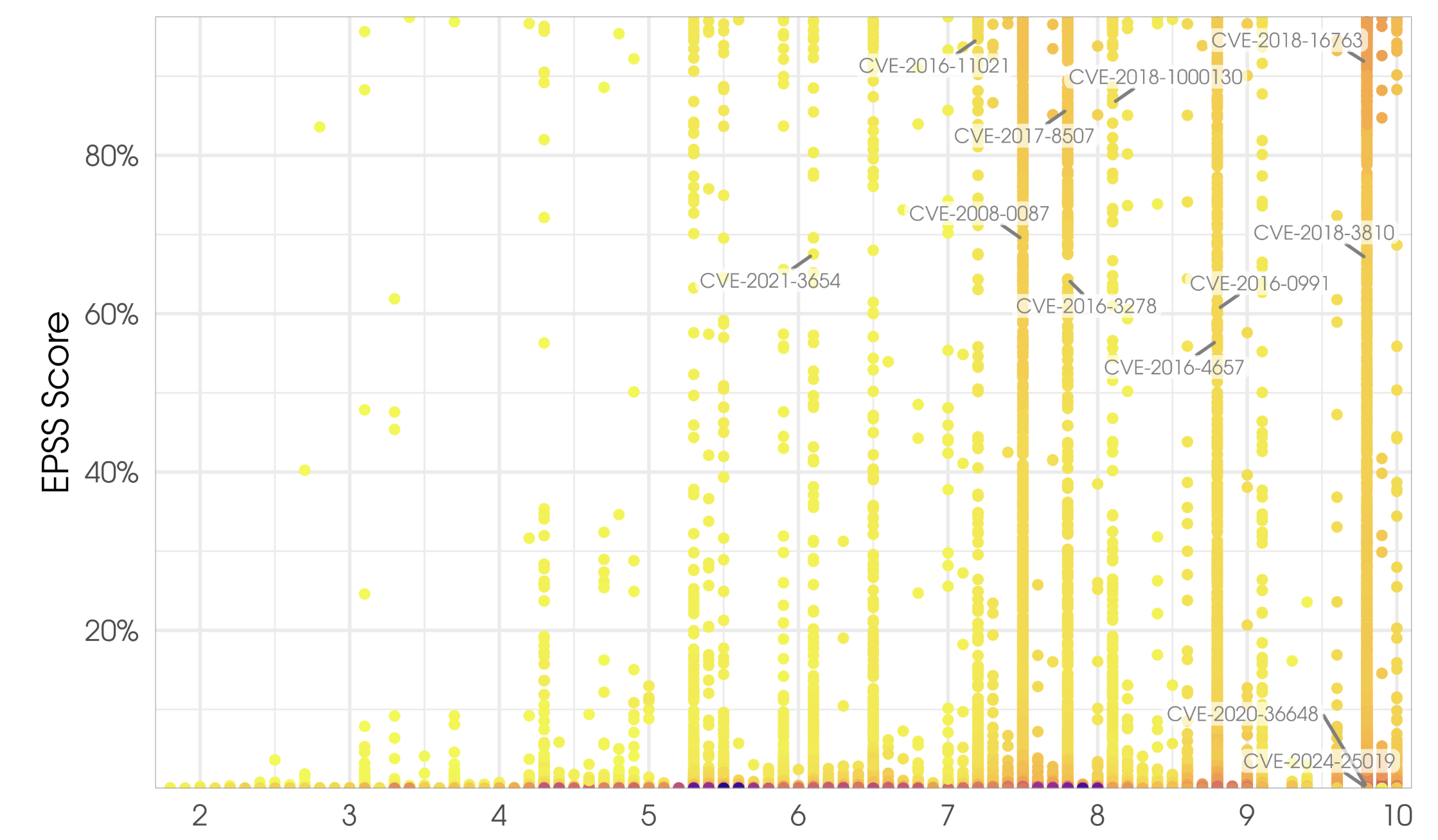
Optimizing Risk Reduction through EPSS-CVSS Integration
EPSS is most effective as a complementary tool rather than a standalone solution. When integrated with CVSS, it creates a powerful prioritization mechanism. By targeting vulnerabilities with both high CVSS severity ratings (Critical/High) and elevated EPSS scores, security teams can optimize their limited resources for maximum risk reduction. This dual-metric approach directly addresses one of the most persistent challenges in vulnerability management: the overwhelming number of theoretically “critical” vulnerabilities competing for finite remediation resources. The combined methodology enables organizations to distinguish between vulnerabilities that are merely severe in theory and those that pose genuine, imminent threats to their environments. Of course, don’t forget to consider the business impact to your systems and applications, according to the organization. The technical risk metrics must be contextualized within your specific business environment
The EPSS Vulnerability Risk Framework
One of the challenges with raw EPSS scores is their daily fluctuation, which can create operational complexity for security teams planning remediation cycles. Additionally, the granular probability scores, while precise, don’t always translate directly into clear action plans. To address these issues and operationalize EPSS effectively, I’ve developed a four-tiered risk categorization system that transforms these dynamic probability scores into stable, actionable remediation guidance:
IMMINENT (EPSS ≥ 0.8 or 80%): These vulnerabilities have at least an 80% probability of exploitation in the next 30 days. They demand immediate attention and should trigger emergency patching protocols for Critical CVSS severity, even outside normal maintenance windows.
ELEVATED (EPSS ≥ 0.5 or 50%): With exploitation probability of 50% or higher, these vulnerabilities represent significant risk. They should be prioritized in the next patch cycle, typically within 7-14 days.
NOTABLE (EPSS ≥ 0.3 or 30%): These vulnerabilities have a considerable chance of exploitation (30% or higher) and warrant inclusion in regular patching schedules, typically within 30 days.
NEGLIGIBLE (EPSS > 0 but < 0.3): While these vulnerabilities have some exploitation potential, the probability is relatively low. They can be addressed through standard maintenance cycles or potentially accepted as risks after proper documentation. It is important to still monitoring these vulnerabilities, as their EPSS scores could change over time.
This framework provides security teams with defensible, data-driven remediation timelines based on actual exploitation likelihood rather than theoretical severity alone. By aligning organizational resources with empirical risk data, teams can focus on what matters most—vulnerabilities attackers are actually targeting.
EPSS Version 4: Refined Risk Assessment
The recent transition from EPSS v3 to v4 represents a significant evolution in vulnerability risk scoring. A comparative analysis of CVE distributions across risk categories reveals important insights about how vulnerabilities in the National Vulnerability Database (NVD) are classified under each version. The following table shows the count of CVEs from NVD as of March 2025 for each risk category:
| Exploit Risk | EPSS v3 | EPSS v4 | Change | % Change |
|---|---|---|---|---|
| IMMINENT (≥80%) | 3,916 | 2,578 | -1,338 | -34.17% |
| ELEVATED (≥50%) | 2,526 | 4,206 | +1,680 | +66.51% |
| NOTABLE (≥30%) | 1,899 | 3,870 | +1,971 | +103.79% |
| NEGLIGIBLE (>0%) | 261,944 | 259,671 | -2,273 | -0.87% |
This redistribution doesn’t indicate a reduction in critical vulnerabilities—rather, it reflects more precise risk calibration. The decrease in IMMINENT-rated vulnerabilities paired with increases in ELEVATED and NOTABLE categories suggests EPSSv4 is less prone to overestimating exploitation likelihood, reducing false positives that can drain valuable security resources.
Implementing the Framework in Your Organization
To successfully adopt this EPSS-based framework:
- Implement EPSS data into vulnerability management platforms and reporting process via API integrations, custom scripts or platform-specific features.
- Establish clear SLAs aligned with the four risk categories.
- Communicate the framework across security, IT operations, and leadership teams.
- Document exceptions where business constraints may require deviations from standard remediation timelines.
- Regularly review remediation metrics to validate the effectiveness of your implementation and make adjustments as needed.
The Business Case: Measurable Security Outcomes
Organizations implementing this EPSS framework typically report several tangible benefits:
- 30-40% reduction in emergency patching by focusing on truly imminent threats
- Improved resource allocation with clearer prioritization guidance
- Enhanced communication with executives through data-driven risk reporting
- More defensible security decisions backed by empirical exploitation data
Conclusion
As vulnerability volumes continue to grow, the ability to prioritize effectively becomes increasingly critical. This EPSS implementation framework provides a structured approach to transforming exploitation probability data into concrete security actions. By aligning remediation efforts with actual threat likelihood, security teams can maximize their impact while optimizing resource utilization.
The journey from EPSS v3 to v4 demonstrates the ongoing refinement of this approach, with each iteration bringing us closer to the goal of truly risk-based vulnerability management. By adopting this framework, organizations can cut through the noise and focus on what matters most—protecting against vulnerabilities attackers are actually targeting.